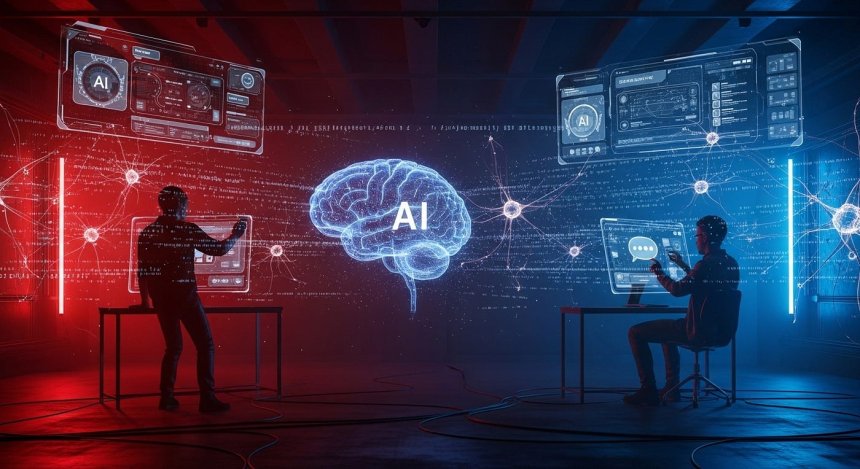
Red teaming is an essential aspect of cybersecurity; it is the emulation of hacking attempts in order to determine the strength of the security position of a particular organization. The introduction: There were methodologies that were traditionally used to identify vulnerabilities, which we call penetration testing, and they were done by human beings. But with the emergence of AI technologies, the cybersecurity horizon has been drastically changed. Use of AI-augmented defenders, which employ the use of machine learning and advanced algorithms, is also increasing to help predict, identify, and mitigate cyber threats. The tools are also able to react to changing threats much quicker than human-based techniques, moving faster to offer a form of defence. The further development of AI leads to the fact that penetration testing becomes more complicated. This development has resulted in more complex cyber-attacks to warrant a further interconnection between human expertise and the capabilities of machines. Although AI has proved to have a lot of potential in automated threat detection, the necessity to merge human knowledge and efficiency with the efficiency of machines is increasingly becoming apparent.

Artificial intelligence (AI) has rocked cybersecurity and is taking center-stage played in improving both offense and defense strategies. Due to the growing popularity of AI tools among defenders (in both threat prediction and mitigation), AI has also become increasingly popular among attackers (as it helps to launch more sophisticated and accurate attacks). Due to the growing use of AI tools in cybersecurity, the efficacy of human versus AI strategies must also be considered, especially in the situation of penetration testing. Artificial intelligence technologies, e.g., automated vulnerability scan tools, anomaly-detecting via machine learning techniques, and predictive threat models, have become a part of security operations. Such instruments assist in identifying potential targets of assault, in addition to responding with warp speed and previously unexampled fidelity to security events.
Modern red teaming practices have severe limitations because of the complexity of cyber threats in this era of modernization. Although penetration testing, which has been done by a group of human agents, has been the core aspect of vulnerability assessment used so far, its efficiency is impaired by the sophistication and expediency of computer attacks. On the other hand, AI-assisted testing tools are more rapid and flexible in their operations but are poor at dealing with complex, non-linear problem-solving situations that involve intuitive knowledge. Although progress has been achieved, there still exists a vacuum of clarity with regard to the capabilities of the integration of AI to red teaming exercises in order to supplement human strategies. The relative absence of scientific literature on the contribution of AI to this area has complicated the production of best practices aiming to combine the knowledge of a human expert and AI tools in the hybrid testing strategy. These gaps need to be addressed in the best interests of maximising penetration testing strategies to improve our defense against complex cyber threats.
Originally based on military strategy, red teaming was employed to re-enact tactics and strategies of the enemy in order to enhance protection preparedness. It is a capability in the cybersecurity domain that has developed to test organizations to see how resilient to the TTPs of opponent organizations by replicating the TTPs of actual adversaries. The history of traditional red teaming entailed rather simple tactics that only human testers were used to penetrate the network of an organization using techniques of social engineering, vulnerability exploitation, and other kinds of attacks. These exercises later evolved, being more promoted, so as to facilitate more professional and diversified attacks, by using elaborate tools and strategies. With the increase in the sophistication of cyber threats, the red teaming techniques were developed to become both offensive and defensive, influencing the evolution of practices in the field of cybersecurity. One of the most important steps occurred in the 1990s when penetration testing became recognized as a more methodical procedure, enabling businesses to assess the vulnerabilities of systems and reinforce them more efficiently.
Traditional red teaming is based on human-driven techniques of penetration testing. Penetration testers, or ethical hackers, simulate real-world cyberattacks to uncover vulnerabilities within an organization's security infrastructure. These tests may either be manual or with automated instruments, yet in the majority, they center on the creativity and problem-solving of human beings. The strategies employed by testers include social engineering, taking advantage of misconfigurations, and playing with network systems to get access to them without any authorization. Nonetheless, human testers do have several drawbacks, particularly when dealing with environments that are quite dynamic and the stakes are high. The complexity and size of the modern infrastructures and their massive interconnectedness are one of the biggest challenges one has to deal with.
Artificial Intelligence (AI) is transforming cybersecurity by offering advanced tools for both defense and offense. With AI in the defense sector, there will be a system that is used to detect, monitor, and react to cyber threats in real time. Such AI tools can take information that consists of large databases and run through it using machine learning algorithms to find its patterns and anomalies, which may mean an attack may occur. AI cannot compare to human pace, but it has the capacity to discover new risks before they become serious, using its quick learning capability and speed in processing information. Moreover, AI processes can serve to automate standard activities related to cybersecurity, thus freeing people to pay attention to the more complicated topics. Nevertheless, offensive application of AI is also of great importance when adversaries start taking advantage of AI to develop more complex and elusive attacks.
The prospects of testing cybersecurity defenses using the tools of AI have generated a paradigm shift when implementing the practice of red teaming. In the traditional context, red teaming in the past used human elements of attack faced in the objective world in order to uncover vulnerabilities in the security systems of an organization. The exercises have changed with the proliferation of AI, leveraging machine learning algorithms and other AI to be able to simulate more advanced and complex attack scenarios. AI tools help improve the iterative nature of red teaming operations to perform these actions more quickly and at a higher frequency. However, with the introduction of AI to this practice, one may question the real usefulness of such practices.

Both human and AI methods have their own advantages and drawbacks in penetration testing. Human testing offers creativity and gut feeling, which helps human testers to discover non-obvious weaknesses and respond dynamically to unexpected obstacles. Human-driven testing may, however, be restricted by experience, time, and the size of the present state of IT environments. AI, in its turn, can deal with great volumes of data and automate routine processes, thus providing the opportunity to cover potential vulnerabilities quickly and more comprehensively. Using AI tools aids in finding previously known vulnerabilities, whether in the form of automated scanners or reinforcement learning agents. In real-life penetration testing scenarios, it can do so efficiently.
Comparing human-to AI-based strategies in red teaming and penetration testing showed their results, identifying the main difference in efficacy. AI-powered tools were on another level concerning the time needed, detectability, and the ability to scale so that vulnerabilities could be established quickly based on existing evidence, and complex attacks could be simulated. Nevertheless, AI was worse than human testers in the cases when creativity, flexibility, and the detection of complex system defects, including business logic errors or people-oriented vulnerabilities, were important. The findings report the necessity of taking an integrated approach of using human understanding and AI tools to streamline red teaming efforts. With the future of AI being likely to leave an immensely significant impact, the incorporation of the mentioned technologies into the work of cybersecurity practitioners can become a step forward in identifying and eliminating new threats. The proposed study is a part of the existing pool of research related to the use of AI and ML in cybersecurity and shall help to improve the understanding of the way in which hybrid red teaming strategies could be used to deepen the protection against intrusions of cybersecurity attackers, shaping new tactics and rising to greater heights.
Future Directions...
Among future studies, one could consider the possibility of mixing AI and human testers in red teaming, with AI assisting in executing mechanical tasks and human testers maintaining strategic control and addressing problems that are not predictable and fixed. Connecting human knowledge with AI would possibly result in more versatile and dynamic penetration testing plans. In the future, with the further evolution of AI technologies, machine learning and reinforcement learning may allow AI systems to be more capable of comprehending new forms of attacks, thus be more adaptive to unforeseen situations. Also, AI-enabled tools may become outstanding in real-time defense systems, enhancing proactive published alerts as well as cutbacks of threats in case of red teaming. The further research will include enhancing AI flexibility and increasing its use in managing human error and organizational weakness, therefore, improving the efficacy of penetration testing and the whole approach to securing cybersecurity.
 Like
0
Like
0
 Dislike
0
Dislike
0
 Love
0
Love
0
 Funny
0
Funny
0
 Angry
0
Angry
0
 Sad
0
Sad
0
 Wow
0
Wow
0